Stand-Alone Devices
- BigDumbDinosaur
- Posts: 9426
- Joined: 28 May 2009
- Location: Midwestern USA (JB Pritzker’s dystopia)
- Contact:
Re: Stand-Alone Devices
Pardon me for being the gruff, old curmudgeon I am, but just what is being discussed here? Is it some sort of secure E-mail algorithm, a 6502 contraption with a USB port, or both? I've completely lost track of what this topic is all about. It's just going around in circles, as far as I can tell.
x86? We ain't got no x86. We don't NEED no stinking x86!
Re: Stand-Alone Devices
Ever get the feeling you're being trolled?
I'm not seeing any evidence of technical competency. Just vague statements, BS about market need and tinfoil hat nonsense.
Does anyone feel different?
I'm not seeing any evidence of technical competency. Just vague statements, BS about market need and tinfoil hat nonsense.
Does anyone feel different?
Re: Stand-Alone Devices
I think the best response to a thread which is no longer interesting is to ignore it. It will go away, or it will attract an audience who do find it interesting.
Re: Stand-Alone Devices
BigEd wrote:
I think the best response to a thread which is no longer interesting is to ignore it.
Re: Stand-Alone Devices
Actually, you're all stuck in the Jim cycle.
1). Post seemingly strange questions to random tech forum.
2). Write an equally strange article on his website.
3). GOTO 1
Example question session on forum:
http://www.python-forum.org/viewtopic.p ... 40&p=45144
Corresponding article:
https://www.futurebeacon.com/python.htm
And now I feel all nasty and mean.
1). Post seemingly strange questions to random tech forum.
2). Write an equally strange article on his website.
3). GOTO 1
Example question session on forum:
http://www.python-forum.org/viewtopic.p ... 40&p=45144
Corresponding article:
https://www.futurebeacon.com/python.htm
And now I feel all nasty and mean.
Re: Stand-Alone Devices
Cray Ze wrote:
Actually, you're all stuck in the Jim cycle.
-
jamesadrian
- Posts: 34
- Joined: 11 Jan 2016
- Location: Rochester, NY 14626
- Contact:
Re: Stand-Alone Devices
Does anybody disagree that the MAX3421 would be a very good choice for a 6502 family USB chip?
Jim Adrian
https://www.futurebeacon.com/jamesadrian.htm
https://www.futurebeacon.com/jamesadrian.htm
-
jamesadrian
- Posts: 34
- Joined: 11 Jan 2016
- Location: Rochester, NY 14626
- Contact:
Re: Stand-Alone Devices
Some comments made recently are not directed toward informing or questioning.
I have made statements and asked questions.
My statements are based on honest and well-motivated research.
My questions are sincere.
If you don't want the device to exist, or you think it is preposterous, there might be something you don't know. Why commit yourself to an attack? Any successful new product is a surprise to somebody.
I have made statements and asked questions.
My statements are based on honest and well-motivated research.
My questions are sincere.
If you don't want the device to exist, or you think it is preposterous, there might be something you don't know. Why commit yourself to an attack? Any successful new product is a surprise to somebody.
Jim Adrian
https://www.futurebeacon.com/jamesadrian.htm
https://www.futurebeacon.com/jamesadrian.htm
- Alarm Siren
- Posts: 363
- Joined: 25 Oct 2016
Re: Stand-Alone Devices
Like many of the others, I honestly do not see a market for this device, beyond a very few crypto-obsessed geeks.
Nevertheless, I'm not going to put you down for wanting to build it - virtually everything I have ever built has, ultimately, been completely useless. That doesn't mean it isn't fun!
However, for encryption and USB, I honestly don't see the 6502 as the right fit. Having taken a quick gander at a C implementation of AES I see numerous uses of Multiplication, Division (or at least, modulus) and relatively large array indexing. Of course, you can do these operations on the 6502 - but only using software and it is therefore comparatively slow. Combine that with the processor topping at 14MHz, in reality usually much lower due to peripheral access rates, and on top of that having a total address space of 64KiB for your USB/filesystem stack, UI code and encryption.... and, to make a complete system, you would need at minimum (without going into FPGAs or Microcontroller-based peripherals) four parts - processor, RAM, ROM and I/O chip of some kind, plus your interfaces for USB and User I/O controls + screen. This thing would probably end up costing in the region of, what, £100-£200 to build including a PCB? if not more?
By comparison the LPC1768 on the mBed platform runs at 96MHz, has an ARM core supporting Multiplication and Division natively, and built-in USB support. In other words, the mBed alone would cover all your needs except for a USB socket and User I/O, and do the whole job considerably quicker. I havn't checked, but there's probably even existing crypto libraries for it. I think they cost about £20. So again, why use the 6502? If you want a "for the hell of it challenge" then yea, fine, but if you actually want to make a product - choose something more practical and cost effective for the job.
Some quick back of the envelope maths:
You mentioned a 1TB external flash drive. If you were able to encrypt one byte of that 1TB per clock cycle, running at that maximum of 14MHz (which, I might add, would be absolutely impossible - for many reasons but least of all that the shortest 6502 instructions take two cycles not one) it would take a little over 19 hours to encrypt that drive in its entirety. That does not sound like a practical product to me.
Nevertheless, I'm not going to put you down for wanting to build it - virtually everything I have ever built has, ultimately, been completely useless. That doesn't mean it isn't fun!
However, for encryption and USB, I honestly don't see the 6502 as the right fit. Having taken a quick gander at a C implementation of AES I see numerous uses of Multiplication, Division (or at least, modulus) and relatively large array indexing. Of course, you can do these operations on the 6502 - but only using software and it is therefore comparatively slow. Combine that with the processor topping at 14MHz, in reality usually much lower due to peripheral access rates, and on top of that having a total address space of 64KiB for your USB/filesystem stack, UI code and encryption.... and, to make a complete system, you would need at minimum (without going into FPGAs or Microcontroller-based peripherals) four parts - processor, RAM, ROM and I/O chip of some kind, plus your interfaces for USB and User I/O controls + screen. This thing would probably end up costing in the region of, what, £100-£200 to build including a PCB? if not more?
By comparison the LPC1768 on the mBed platform runs at 96MHz, has an ARM core supporting Multiplication and Division natively, and built-in USB support. In other words, the mBed alone would cover all your needs except for a USB socket and User I/O, and do the whole job considerably quicker. I havn't checked, but there's probably even existing crypto libraries for it. I think they cost about £20. So again, why use the 6502? If you want a "for the hell of it challenge" then yea, fine, but if you actually want to make a product - choose something more practical and cost effective for the job.
Some quick back of the envelope maths:
You mentioned a 1TB external flash drive. If you were able to encrypt one byte of that 1TB per clock cycle, running at that maximum of 14MHz (which, I might add, would be absolutely impossible - for many reasons but least of all that the shortest 6502 instructions take two cycles not one) it would take a little over 19 hours to encrypt that drive in its entirety. That does not sound like a practical product to me.
Want to design a PCB for your project? I strongly recommend KiCad. Its free, its multiplatform, and its easy to learn!
Also, I maintain KiCad libraries of Retro Computing and Arduino components you might find useful.
Also, I maintain KiCad libraries of Retro Computing and Arduino components you might find useful.
-
jamesadrian
- Posts: 34
- Joined: 11 Jan 2016
- Location: Rochester, NY 14626
- Contact:
Re: Stand-Alone Devices
Alarm Siren,
Thank you very much for your recent message.
It seems that it may be more cost effective to use a microprocessor other than the 65816. I had assumed that the 6502 family devices were cheaper than the others and that the slowness is not an issue. You mentioned multiplication and division. I would not use those operations. I would use the XOR operation.
I don't know off hand how long it would take a 65816 to write a file that is the XOR of two other files, each being one megabyte in size, but most text email messages are much shorter. I want to produce the least expensive device.
The one-time pad has never been cracked. In 1950 or 1949 Claude Shannon proved that this algorithm can never be cracked if it is done correctly. From the wiretapper's point of view, every possible message of the length of the one being hacked is equally likely to be the intended message.
The strongest encryption method is the simplest.
For decades, the naysayers insisted that the one-time pad was too inconvenient. Now we have one terabyte flash drives. This enables the encryption of one-megabyte messages, one per day, for a million days. The sharing of one flash drive in secret between the sender and the receiver can maintain secure email communication for decades. It only takes one secure delivery.
Every other encryption method has been cracked.
Truly secure encryption depends on shared secrets. The methods made popular depend on complexity or obscure math or both and do not depend on truly random data shared by the sender and receiver only.
Many people have more than one computing device. Many people have seen an advertising message on their desktop before invoking their browser. Public education on the matter is not beyond practicality. It is not beyond me.
If there is a cheaper way to make what I have described, I am all for it. If the argument is that a more expensive device will provide service beyond the requirements of the stated goal, I am not for it.
I would still like to know if there is a consensus about the USB controller choice.
I appreciate your thoughtful message.
Thank you very much for your recent message.
It seems that it may be more cost effective to use a microprocessor other than the 65816. I had assumed that the 6502 family devices were cheaper than the others and that the slowness is not an issue. You mentioned multiplication and division. I would not use those operations. I would use the XOR operation.
I don't know off hand how long it would take a 65816 to write a file that is the XOR of two other files, each being one megabyte in size, but most text email messages are much shorter. I want to produce the least expensive device.
The one-time pad has never been cracked. In 1950 or 1949 Claude Shannon proved that this algorithm can never be cracked if it is done correctly. From the wiretapper's point of view, every possible message of the length of the one being hacked is equally likely to be the intended message.
The strongest encryption method is the simplest.
For decades, the naysayers insisted that the one-time pad was too inconvenient. Now we have one terabyte flash drives. This enables the encryption of one-megabyte messages, one per day, for a million days. The sharing of one flash drive in secret between the sender and the receiver can maintain secure email communication for decades. It only takes one secure delivery.
Every other encryption method has been cracked.
Truly secure encryption depends on shared secrets. The methods made popular depend on complexity or obscure math or both and do not depend on truly random data shared by the sender and receiver only.
Many people have more than one computing device. Many people have seen an advertising message on their desktop before invoking their browser. Public education on the matter is not beyond practicality. It is not beyond me.
If there is a cheaper way to make what I have described, I am all for it. If the argument is that a more expensive device will provide service beyond the requirements of the stated goal, I am not for it.
I would still like to know if there is a consensus about the USB controller choice.
I appreciate your thoughtful message.
Jim Adrian
https://www.futurebeacon.com/jamesadrian.htm
https://www.futurebeacon.com/jamesadrian.htm
- Alarm Siren
- Posts: 363
- Joined: 25 Oct 2016
Re: Stand-Alone Devices
How are you going to generate this 1TB of genuinely random data? Are you proposing that everyone on earth exchanges 1TB shared secrets with every other person on earth? How does the receipient know what offset to use from the beginning of that shared secret drive? How does the sender ensure that they never, ever reuse the same chunk of one-time pad (a requirement for true security in one-time pad)? How does the receiver know that they have successfully decoded the message correctly? How does the recepient verify the authenticity and integrity of the message (i.e. how do they know it came from who it claims to be from, and how do they know it has not been modified in transit)? How do you get the encrypted message to and from the device - surely you're not expecting the user to manually copy out a megabyte of gobbledegook between their internet enabled computer and this encrypting box?
I know the answers to most if not all of those, and in most cases it is either "You simply don't - its impractical" or "you need something more complicated than XOR". These questions, and others besides, are why one-time pad is not normally used in practice. Whilst I agree that theoretically secure is better than computationally secure, in practice computationally secure is "good enough" on the basis that by the time you can crack it, the information is no longer useful. And that's all that you really need from encryption - to make the resources or time required to read the message an order of magnitude greater than the value of the information. I can trivially decrypt messages encoded using the Engima cipher 70 years ago - but it doesn't matter that I can because those messages contain nothing of value anymore, except perhaps purely for historical interest. Nothing encrypted today using modern, properly implemented cipher techniques can be cracked in the next ten years, by which time anything that you or I would write in them will be completely irrelevant - assuming what you write isn't a confession to a murder or some-such.
I know. Not only do you keep repeating it, as if we havn't read what you said, but I also studied cryptography at University.
I don't knoe either, XOR itself is easy, but copying data into and out of the USB will use a lot of cycles, as will other periphial processing. If I throw a wild guesstimate of an average of 200 cycles per byte, that means we need 200million cycles to complete the job. 200million / 14MHz = 14.28 seconds. I honestly think, however, in practice it'd probably be more like a minute or two as any system you build it unlikely to operate at 14MHz, or if it does, not all the time, and I suspect that 200 cycles per byte is on the low end of possibility, given how complex I know USB and filesystems to be in the PC market.
The LPC1768 costs £8.43. That can do 96MHz (maybe evne higher, I havn't checked), has built in 32K RAM, 512K Flash and USB support. The nearest equivalent in the 65xx range is probably the W65C265S, costing £12.21, max speed 8MHz, no native USB support and 576 bytes of RAM. It has 8KB of ROM, but I don't think that'd be usable for your own software in practice as I think its mask programmed in the factory. So, it costs £4 more, is considerably slower and lacks useful functionality for your intended job, which you'd need to supply externally as an extra part, further increasing costs.
This is ignoring the modern phenominom of Forward Secrecy. Essentially modern public key encryption is increasingly using a system whereby hacking the encryption stream after the fact will not provide enough information to allow the message stream to be read, so reading the stream requires intercepting and decoding the stream in real time, which no-one on earth currently has the capacity to do, and will not do for the forseeable future. A far bigger problem, infact, is MitM attacks revolving around the inhernetly flawed PKI trust architecture. There are solutions to PKI, principally web-of-trust, they've just never taken off because they require people to be an active participant in their own security, which most people don't want to be because "effort".
With the greatest possible respect, it is beyond you. The entire tech security industry as a whole has been trying to educate the average joe about these sorts of things for literally decades and, if anything, they've actually made the problem worse as people get a false sense of security when they follow some handy guide without actually understanding the theory behind it. And that's assuming they even do that, most people simply ignore all advice if it inconveniences them even slightly. How many people use "password" as their password, or leave devices setup to defaults? Who actually checks the SSL certificates on the sites they visit? Who spends the time to encrypt their local computer drives? How many times have you read about some idiot civil-servant leaving a USB full of unencrypted personal details on a train?
The tools and the knowledge are there, but people choose to ignore it. To get the average person to use encryption, it has to be as transparent to them as possible, which means they cannot be an active participant in it, which means that shared secrets in the way you describe are not practical because people simply won't do it.
Besides, are you going to ring up Microsoft, Apple, Google and the myriad other OS makers and get them all to put a message into their OSs that tells people to buy your encryption box? Best of luck with that, but it ain't gonna happen, not unless you have several billion pounds to throw into their bottomless money holes. Plus, these big companies don't actually want you to be truly secure, because if you were they couldn't datamine you, they only pay lip-service to security because it gets them more money (or prevents loss of money from fines).
FINALLY, on one final note, if some boogey-man really wants to find out what your encrypted message says...
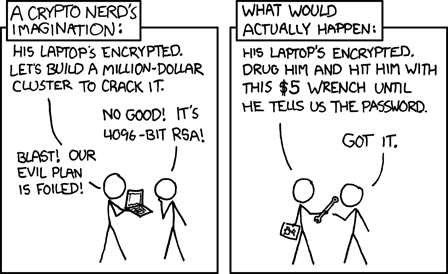
...
Wow, that ended up longer than I planned, and its 3:15am. I'm going to bed
I know the answers to most if not all of those, and in most cases it is either "You simply don't - its impractical" or "you need something more complicated than XOR". These questions, and others besides, are why one-time pad is not normally used in practice. Whilst I agree that theoretically secure is better than computationally secure, in practice computationally secure is "good enough" on the basis that by the time you can crack it, the information is no longer useful. And that's all that you really need from encryption - to make the resources or time required to read the message an order of magnitude greater than the value of the information. I can trivially decrypt messages encoded using the Engima cipher 70 years ago - but it doesn't matter that I can because those messages contain nothing of value anymore, except perhaps purely for historical interest. Nothing encrypted today using modern, properly implemented cipher techniques can be cracked in the next ten years, by which time anything that you or I would write in them will be completely irrelevant - assuming what you write isn't a confession to a murder or some-such.
Quote:
The one-time pad has never been cracked. In 1950 or 1949 Claude Shannon proved that this algorithm can never be cracked if it is done correctly. From the wiretapper's point of view, every possible message of the length of the one being hacked is equally likely to be the intended message.
Quote:
I don't know off hand how long it would take a 65816 to write a file that is the XOR of two other files, each being one megabyte in size, but most text email messages are much shorter.
Quote:
I had assumed that the 6502 family devices were cheaper than the others
Quote:
The methods made popular depend on complexity or obscure math or both and do not depend on truly random data shared by the sender and receiver only.
Quote:
Many people have more than one computing device. Many people have seen an advertising message on their desktop before invoking their browser. Public education on the matter is not beyond practicality. It is not beyond me.
The tools and the knowledge are there, but people choose to ignore it. To get the average person to use encryption, it has to be as transparent to them as possible, which means they cannot be an active participant in it, which means that shared secrets in the way you describe are not practical because people simply won't do it.
Besides, are you going to ring up Microsoft, Apple, Google and the myriad other OS makers and get them all to put a message into their OSs that tells people to buy your encryption box? Best of luck with that, but it ain't gonna happen, not unless you have several billion pounds to throw into their bottomless money holes. Plus, these big companies don't actually want you to be truly secure, because if you were they couldn't datamine you, they only pay lip-service to security because it gets them more money (or prevents loss of money from fines).
FINALLY, on one final note, if some boogey-man really wants to find out what your encrypted message says...
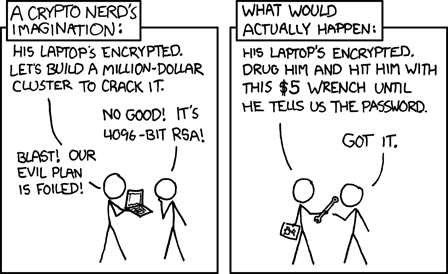
...
Wow, that ended up longer than I planned, and its 3:15am. I'm going to bed
Want to design a PCB for your project? I strongly recommend KiCad. Its free, its multiplatform, and its easy to learn!
Also, I maintain KiCad libraries of Retro Computing and Arduino components you might find useful.
Also, I maintain KiCad libraries of Retro Computing and Arduino components you might find useful.
- BigDumbDinosaur
- Posts: 9426
- Joined: 28 May 2009
- Location: Midwestern USA (JB Pritzker’s dystopia)
- Contact:
Re: Stand-Alone Devices
Alarm Siren wrote:
You mentioned a 1TB external flash drive. If you were able to encrypt one byte of that 1TB per clock cycle, running at that maximum of 14MHz (which, I might add, would be absolutely impossible - for many reasons but least of all that the shortest 6502 instructions take two cycles not one) it would take a little over 19 hours to encrypt that drive in its entirety. That does not sound like a practical product to me.
x86? We ain't got no x86. We don't NEED no stinking x86!
-
jamesadrian
- Posts: 34
- Joined: 11 Jan 2016
- Location: Rochester, NY 14626
- Contact:
Re: Stand-Alone Devices
It is a waste of time to disagree on the facts.
Good bye.
Good bye.
Jim Adrian
https://www.futurebeacon.com/jamesadrian.htm
https://www.futurebeacon.com/jamesadrian.htm
-
DerTrueForce
- Posts: 483
- Joined: 04 Jun 2016
- Location: Australia
Re: Stand-Alone Devices
If you're still here, jamesadrian,
I'm in the "agreed to disagree" camp, for the record. I don't think there's much market opportunity for it, but if you want to build your thing, by all means go ahead.
BUT: I would pick a USB controller, and run with it. The worst that'll happen is you'll waste a bit of time and a bit of money on your development costs. I went and bought a bunch of 74-series logic chips, and I ended up replacing them with a PLD. Wasted about $30-$50, but they can be reused.
I'm in the "agreed to disagree" camp, for the record. I don't think there's much market opportunity for it, but if you want to build your thing, by all means go ahead.
BUT: I would pick a USB controller, and run with it. The worst that'll happen is you'll waste a bit of time and a bit of money on your development costs. I went and bought a bunch of 74-series logic chips, and I ended up replacing them with a PLD. Wasted about $30-$50, but they can be reused.